Overview
Properly configured SSIDs are foundational to a secure, high-performing wireless network. This guide covers recommended SSID configurations for Meter networks—including default SSIDs every network should have, optional SSIDs for specific use cases, and the settings that should be applied across all deployments.
These best practices apply to network administrators configuring SSIDs through the Dashboard. If you need to deviate from these guidelines, contact Support Engineering for guidance.
Prerequisites
- Access to the Meter Dashboard with write permissions
- VLANs configured for your network (see VLANs)
- Familiarity with creating and editing SSIDs
Use cases
- Setting up a new Meter network and configuring SSIDs for the first time
- Auditing an existing network for SSID security and segmentation issues
- Adding SSIDs for specialized device types such as IoT, AV, or security cameras
- Transitioning from WPA2 to WPA3 across your wireless network
Default SSIDs
The following SSIDs should be configured on every Meter network. SSID and VLAN names can be customized—for example, the employee SSID can use your company name—but the configuration guidelines below should be followed.
Employee
| Setting | Recommendation |
|---|---|
| Frequency bands | 5 GHz and 6 GHz only |
| VLAN | Private (or customer-specified) |
| Security | WPA3-Personal or WPA3-Enterprise. Use WPA3-Transition if legacy devices require it |
| Routing | Can route to other VLANs, but should not route to the Guest VLAN |
The employee SSID is the primary network for your organization's staff and trusted devices. Assign it to the Private VLAN or another VLAN specified for your environment.
Guest
| Setting | Recommendation |
|---|---|
| Frequency bands | 5 GHz and 6 GHz only |
| VLAN | Guest (or customer-specified) |
| Security | WPA3-Transition with a password. Captive portal is optional |
| Additional settings | Show on guest.meter.network, client isolation enabled |
The guest SSID provides internet access for visitors while isolating them from your internal network. This SSID is almost always configured with a password.
IoT
| Setting | Recommendation |
|---|---|
| Frequency bands | 2.4 GHz and 5 GHz |
| VLAN | IoT-specific VLAN, isolated from Employee |
| Security | WPA2-Personal |
The IoT SSID is dedicated to devices that need a 2.4 GHz connection but may also use 5 GHz. IoT devices are inherently less secure and can introduce risks to internal networks if not properly segmented.
If 2.4 GHz-only devices need to route to the employee network, a separate 2.4 GHz + 5 GHz SSID can be configured for them.
Non-default SSIDs
The following SSIDs may be configured depending on your environment. These are common examples and will vary by industry and use case.
Security
For camera systems and door access control. This SSID should be assigned a dedicated VLAN with tight access restrictions—only key personnel should have access.
| Setting | Recommendation |
|---|---|
| Frequency bands | 2.4 GHz and 5 GHz |
| VLAN | Security |
AV (audio/video)
For audio and video equipment that requires Wi-Fi. Most AV equipment is hardwired, but some may need wireless access. AV devices do not have the tight restrictions of security devices and can often use the IoT SSID instead.
| Setting | Recommendation |
|---|---|
| Frequency bands | 5 GHz only (unless devices only support 2.4 GHz) |
| VLAN | AV |
If a dedicated AV SSID is not required, use the IoT SSID.
Faculty and student
Common in schools and universities. The Faculty SSID functions similarly to the Employee SSID, while the Student SSID provides segmented access for students.
| SSID | VLAN |
|---|---|
| Faculty | Faculty (or Private) |
| Student | Student |
Dynamic VLAN
A single SSID that uses RADIUS attributes to assign users to the correct VLAN based on their credentials. This approach segments the network using one SSID instead of many.
See Dynamic VLANs for configuration details.
Default SSID settings
The following settings should be applied across all SSIDs unless there is a specific reason to deviate.
| Setting | Recommendation |
|---|---|
| Minimum basic data rate | 24 Mbps for 5 GHz and 6 GHz. 11 Mbps for 2.4 GHz. Warehouse and manufacturing environments should use 12 Mbps on 5 GHz and 11 Mbps on 2.4 GHz |
| 802.11k/v | Enabled on all SSIDs. Supported by most clients and improves roaming performance |
| RTS/CTS | Enabled by default. Essential for legacy device communication and avoiding hidden-node issues |
| 802.11r | Enable only for WPA2-Enterprise and WPA3-Enterprise networks. Provides no benefit for Personal SSIDs |
| Multicast-to-unicast | Enabled with a default threshold of 15 clients. Converts multicast frames to unicast to improve airtime efficiency. Automatically disables when the client count exceeds the threshold |
| 2.4 GHz allocation | Dedicate 2.4 GHz solely to the IoT SSID. All other SSIDs should use 5 GHz and 6 GHz only unless specifically required |
| VLAN assignment | Each SSID must have a unique VLAN. Avoid assigning the same VLAN to multiple SSIDs unless there is a specific, documented reason |
| WPA3 | Use WPA3 on all SSIDs unless specifically requested otherwise. WPA3 is required for Wi-Fi 7 operation. If devices cannot connect to WPA3, configure a WPA3-Transition SSID or use the IoT network with WPA2-Personal |
| Proxy ARP | Enabled. The access point maintains an IP-to-MAC address mapping and responds to ARP requests on behalf of clients, reducing ARP turnaround time |
Optional SSID settings
The following settings should only be configured for specific use cases. Contact Support Engineering if you are unsure whether these settings are appropriate for your environment.
| Setting | Description | Considerations |
|---|---|---|
| Hidden SSID | Prevents the SSID from appearing in Wi-Fi network lists | Not a security feature—SSIDs are easily discovered with network scanning tools. Hiding an SSID forces clients to rely on active scanning only, which can make connections less reliable. Only enable if specifically requested |
| 802.11w | Protects management frames from spoofing and eavesdropping | WPA3 and Wi-Fi 7 use 802.11w automatically. Only enable manually when using Wi-Fi 6 and additional security is required. Can prevent legacy clients from connecting |
| 802.11ax | Disables Wi-Fi 5 (802.11ac) compatibility | Only enable when all clients support Wi-Fi 6 or later |
| 802.11r | Fast BSS transition for faster roaming | Only use with WPA2-Enterprise or WPA3-Enterprise SSIDs |
| Client isolation | Prevents clients from communicating with each other on the same SSID | Enable only for guest networks or highly secure networks at the customer's request |
Example: misconfigured SSIDs
The screenshot below is from an example deployment and illustrates several common configuration mistakes.
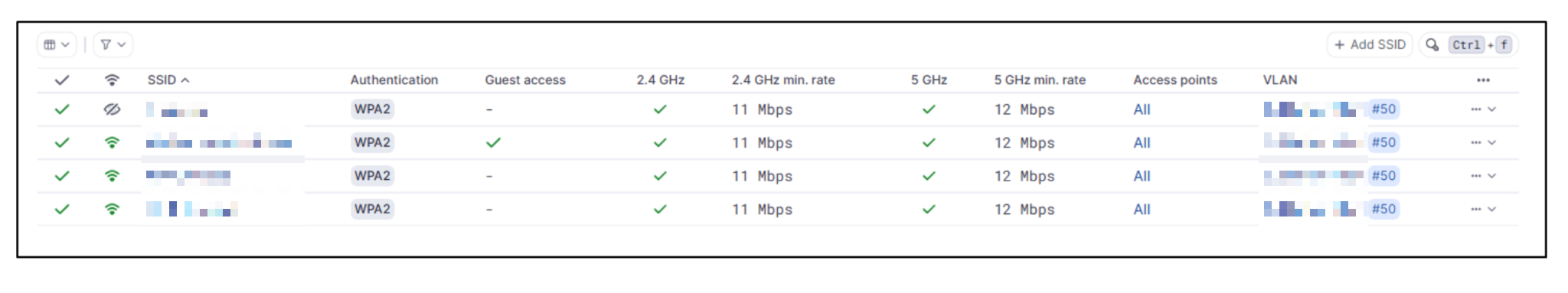
Issues identified:
- All SSIDs use WPA2-Personal — WPA3-Personal or WPA3-Enterprise should be used for stronger security
- All SSIDs broadcast on both 2.4 GHz and 5 GHz — Only the IoT SSID should use 2.4 GHz. Broadcasting all SSIDs on 2.4 GHz can cause clients to connect to a slower frequency band
- All SSIDs are assigned to the same VLAN — Each SSID should have its own VLAN. Sharing a VLAN between employee and guest SSIDs allows guests to access the same subnet as employees, which is a significant security risk
Best practices summary
- Use WPA3 on all SSIDs. Fall back to WPA3-Transition only when legacy devices require it
- Reserve 2.4 GHz for IoT devices. Configure all other SSIDs for 5 GHz and 6 GHz only
- Isolate guest networks with a dedicated VLAN, client isolation, and no routing to internal VLANs
- Segment IoT devices on a dedicated VLAN isolated from the employee network
- Enable 802.11k/v on all SSIDs to improve client roaming
- Enable RTS/CTS by default to support legacy devices and prevent hidden-node issues
- Keep the number of SSIDs minimal. Each additional SSID consumes airtime. Use Dynamic VLANs when you need to segment many user groups
Related resources
Need help?
If you run into any issues or have questions, please reach out to our Support Engineering team by opening a ticket via the Dashboard: https://dashboard.meter.com/support
Last updated by Meter Support Engineering on 03/06/2026